Bio

I am an Internet researcher with a background in protocol deployment and
measurement, currently working at Fastly.
I focus on Internet protocol behaviour and evolution. I am especially
interested in IPv6 deployment and the inherent challenges. Relatedly, I am
interested in continued evolution: QUIC, DNS over HTTPS, RPKI, DNSSEC, and the
various privacy problems they each solve.
I speak frequently and attend some IETF meetings and research conferences. I
write about Internet technologies to help encourage operational experience.
I received my Ph.D. in Computing Science from the University of Glasgow in
2012, and my M.Sci. from the same institution in 2005. Since then, I have led
the team building network monitoring agents hosted on tens of thousands of
disparate hosts at Boundary, managed the rollout of IPv6 at Yahoo on
properties with hundreds of millions of users, and engaged in R&D at the RIPE NCC.
Recent Talks
Research
I study protocol development and deployment, and how we measure those. I am
particularly interested in IPv6 development, transition technologies, and the
security gaps the transition presents.
A complete list of publications is available on my CV.
Selected Peer-Reviewed Publications
-
Withdrawal Symptoms: Filtering of Announcements from a Route Collector System
S.D. Strowes, R. Wilhelm, E. Aben
ACM, IRTF & ISOC Applied Networking Research Workshop (ANRW) 2020
-
Debogonising 2a10::/12: Analysis of one week’s visibility of a new /12
S.D. Strowes, R. Wilhelm, F. Obser, R. Stagni, A. Formoso, E. Aben
[Slides: keynote, pdf]
[Video]
Network Traffic Measurement and Analysis Conference (TMA) 2020
-
A Long Way to the Top: Significance, Structure, and Stability of Internet Top Lists
Q. Scheitle, O. Hohlfeld, J. Gamba, J. Jelten, T. Zimmermann, S.D. Strowes, N. Vallina-Rodriguez
[Slides: pdf] [Video]
ACM SIGCOMM Internet Measurement Conference (IMC) 2018
Awarded: Community Contribution Award
-
Clusters in the Expanse: Understanding and Unbiasing IPv6 Hitlists
O. Gasser, Q. Scheitle, P. Foremski, Q. Lone, M. Korczynski, S.D. Strowes, L. Hendriks, G. Carle
ACM SIGCOMM Internet Measurement Conference (IMC) 2018
-
Diurnal and Weekly Cycles in IPv6 Traffic
S.D. Strowes
ACM, IRTF & ISOC Applied Networking Research Workshop (ANRW) 2016
-
An Experimental Study of Home Gateway Characteristics
S. Hätönen, A. Nyrhinen, L. Eggert, S. Strowes, P. Sarolahti, and M. Kojo
ACM SIGCOMM Internet Measurement Conference (IMC) 2010
Selected Articles
About
I work actively to encourage the deployment of IPv6. Between 2014 and 2016,
I led IPv6 deployment at Yahoo.
Deployment at a global scale brings tough problems: analytics and network-level
debugging, purchasing decisions and network architecture, liasing with vendors
to remove or work around bugs, security issues, and challenges for
application or library developers. Coordinating so many distinct teams was no
easy task, but we enabled IPv6 on many properties, bringing IPv6 quietly to
millions of users.
If you are interested in working on your own IPv6 transition, please reach out.
About
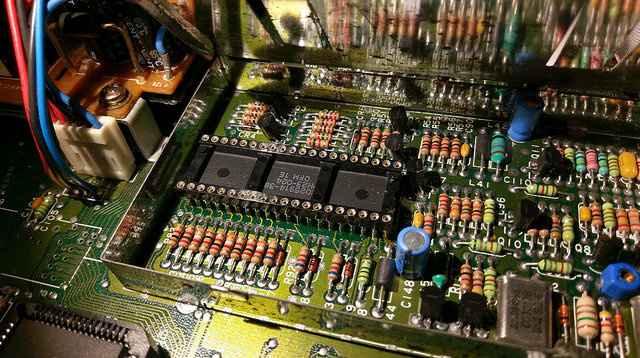
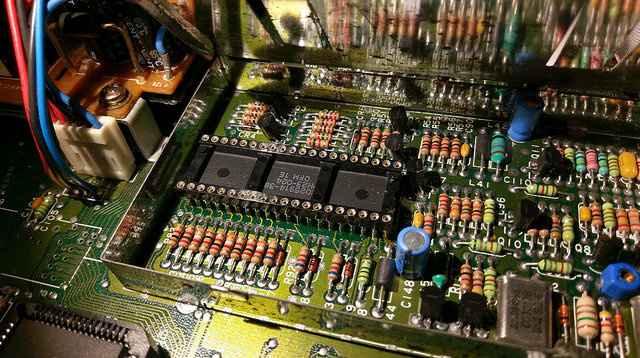
I maintain Atari ST-era hardware and software: I restore and refurbish
hardware, and I archive floppy disks with a KryoFlux floppy controller. I am
interested in elongating the lives of these machines and keeping them
running.
I file photos on
Flickr, and I have written KryoFlux format
parsers to help me debug bad floppy reads.
Contact